A NEW FRONTIER IN FUZZING
REAL-TIME VIDEO DETECTION FOR CAN BUS NETWORKS
Introduction
My MSc dissertation introduces a revolutionary approach to fuzzing, combining video-based detection with traditional CAN bus fuzzing techniques, offering unprecedented insight into how modern vehicles respond to malicious CAN messages.
In this paper, I explored not just how systems log crashes or errors, but how visual feedback from the instrument cluster—from flickering warning lights to erratic gauge movements—reveals deeper vulnerabilities. These are issues that conventional fuzzing tools simply overlook. What started as a simple idea turned into a project that pushes the boundaries of automotive cybersecurity, and perhaps, the broader domain of cyber-physical systems security.
The Beginning: Overcoming Hurdles
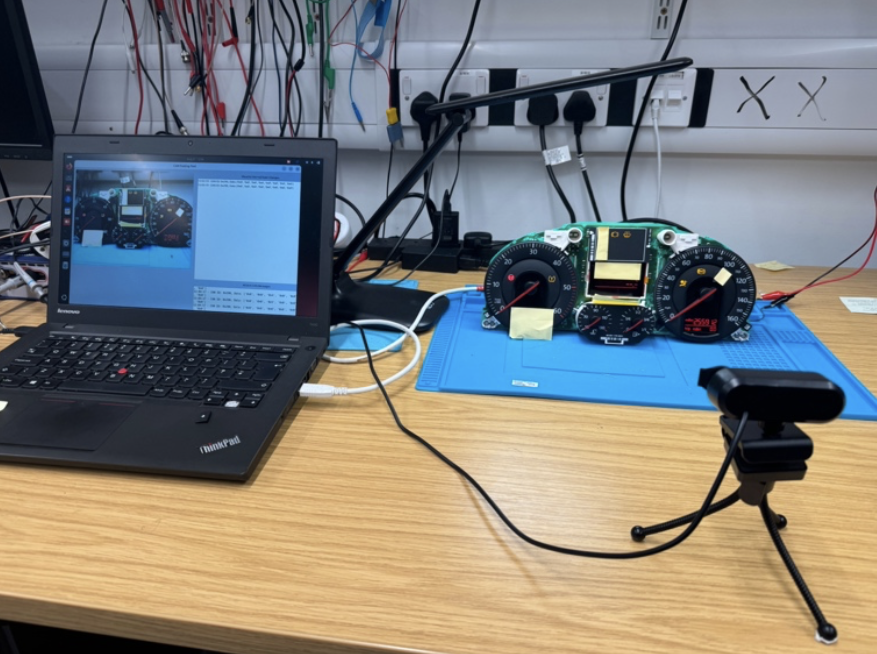
The project wasn’t without its struggles. One of the first challenges was assembling the hardware setup. Working with a Volkswagen Passat instrument cluster and a PCAN-USB adapter, I spent countless hours meticulously wiring the system together. The limited documentation available for these components posed a major hurdle, but I persisted. With the help of industry experts from TCS, ZF Technologies, and Jaguar Land Rover, I was able to correctly map the cluster’s pinout and establish communication over the CAN bus.
It was during these early trials that I noticed how visually captivating the instrument cluster’s responses were to the CAN messages being fuzzed. This gave me the inspiration to go beyond traditional log-based fuzzing and look at how visual cues could provide a window into hidden vulnerabilities.
The Power of Video Detection
Once the hardware was functional, I began developing the video detection algorithm. My initial plan was to rely solely on image detection. However, it quickly became apparent that static image processing wasn’t fast enough to catch the subtle yet important changes happening in real time, such as the rapid flashing of warning lights or the erratic movements of the tachometer needle.
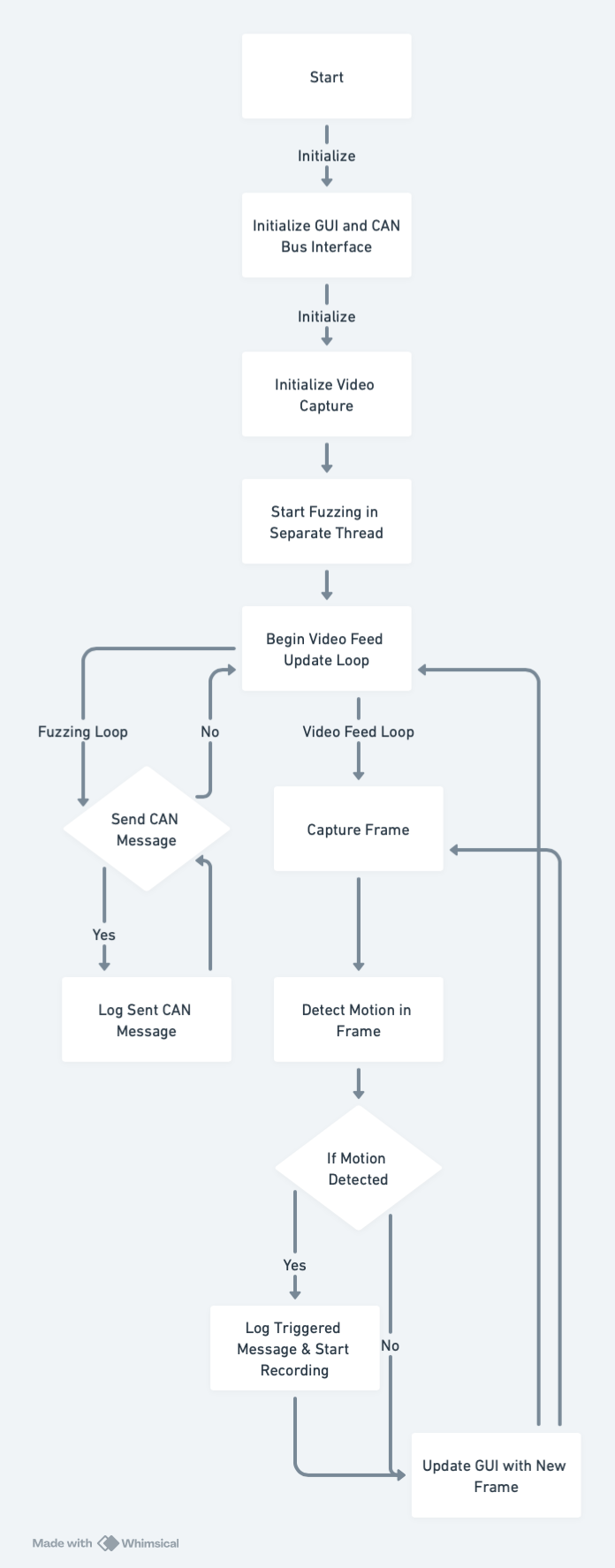
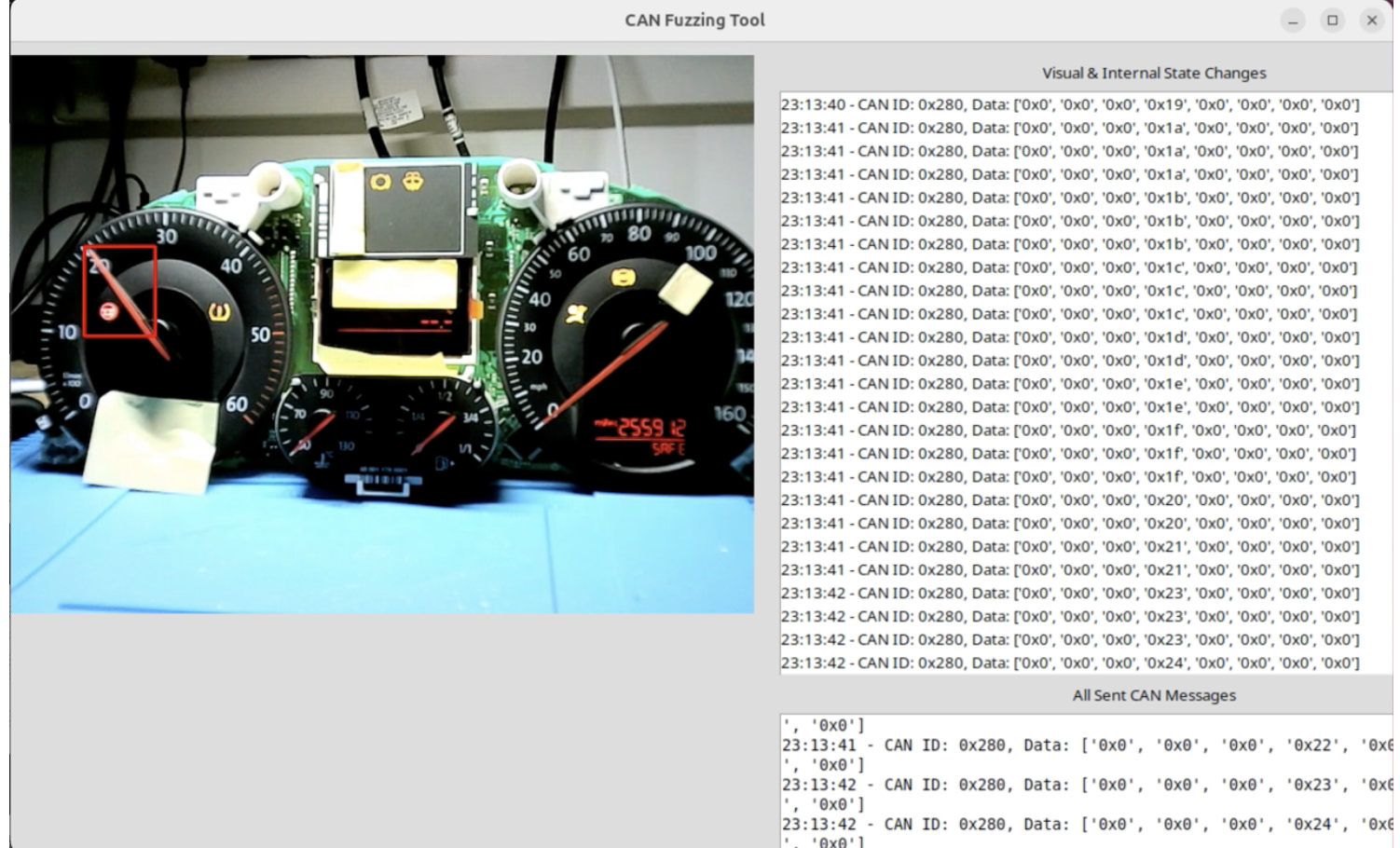
This realization pushed me toward designing a real-time video detection system. By integrating this into the fuzzing tool, I was able to capture a broader range of changes—those quick, almost imperceptible alterations that can signal a significant issue. The OpenCV-based detection algorithm would run continuously, monitoring every frame of the video feed for anomalies. Every time a change was detected, the system logged the corresponding CAN message, enabling me to trace each visual reaction back to its cause.
Discovering Hidden Indicators
The power of this approach became evident as I began uncovering a variety of previously undetected anomalies. For instance, one of the most intriguing findings was that sending a CAN message with ID 0x280 and values in the 4th byte caused the tachometer needle to behave erratically. This was something that would have been difficult, if not impossible, to detect through logs alone.
This gave a understanding that each byte contains a data value which has role/function that could possibly be used to map a Control Flow Diagarm of the of the Whole CAN Bus Network.
But it wasn’t just the tachometer that revealed secrets. During the testing phase, I discovered that messages 0x50 to 0x51 triggered the seatbelt warning light and power steering warning. These indicators flickered on and off in rapid succession, as captured in the video feed. It was here that the video-based fuzzing tool truly shined, allowing me to pinpoint the exact messages responsible for each warning, even in the midst of a flood of CAN traffic.
The Bigger Picture
The deeper I dove into the project, the more I realized that this approach was opening doors to entirely new possibilities. While my focus had been on the instrument cluster of a single vehicle, the implications of this work are far-reaching. Video-based fuzzing can be applied to other sectors where visual feedback is integral—such as industrial control systems, medical devices, and aviation. In any system where the interaction between physical components and digital control signals exists, this method can unveil hidden vulnerabilities.
In my paper, I’ve documented additional findings, including CAN messages that trigger less obvious anomalies. These include unusual changes in the fuel gauge, as well as unexpected traffic from CAN ID 0x320. This wealth of data points to a new frontier in fuzzing, where visual and log-based analysis come together to provide a more comprehensive security assessment
Conclusion: A New Approach to Fuzzing
This work marks a significant shift in how we approach fuzzing, particularly in automotive cybersecurity. By fusing real-time video detection with CAN bus fuzzing, I have developed a tool that not only finds log-based vulnerabilities but also visual anomalies—those subtle signs that something is wrong, hidden in plain sight.
With this research, I hope to contribute to the growing field of cyber-physical systems security and inspire others to explore how video detection can be applied to uncover vulnerabilities in other industries. If you want to discuss more about it, feel free to reach out to me!
I want to extend my deepest gratitude to Professor Tom Chothia for his guidance throughout this project. His insights were invaluable, pushing me to expand the scope of my research and explore new methods. I also want to thank Dr. Andreea Ina Radu, Thompson Martin, and John Wong for their technical support and feedback.
Tools & Technologies
- CAN Bus Communication
- Python
- OpenCV
- Wireshark
- Automotive ECUs